A Maryland defense attorney has decided to challenge the conviction of one of his clients after it was recently discovered that the phone cracking product used in the case, produced by digital forensics firm Cellebrite, has severe cybersecurity flaws that could make it vulnerable to hacking.
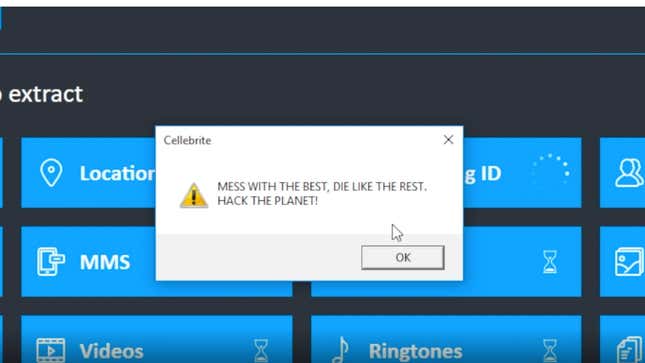
Ramon Rozas, who has practiced law for 25 years, told Gizmodo that he was compelled to pursue a new trial after reading a widely shared blog post written by Moxie Marlinspike, the CEO of encrypted chat app Signal. It was just about a week ago that Marlinspike brutally dunked on Cellebrite—writing, in a searing takedown, that the company’s products lacked basic “industry-standard exploit mitigation defenses,” and that security holes in its software could easily be exploited to manipulate data during cell phone extraction.
Given the fact that Cellebrite’s extraction software is used by law enforcement agencies the world over, questions have naturally emerged about the integrity of investigations that used the tech to secure convictions.
For Rozas, the concerns center around the fact that “Cellebrite evidence was heavily relied upon” to convict his client, who was charged in relation to an armed robbery. The prosecution’s argument essentially turned on that data, which was extracted from the suspect’s phone using the company’s tools. In a motion recently filed, Rozas argued that because “severe defects” have since been uncovered about the technology, a “new trial should be ordered so that the defense can examine the report produced by the Cellebrite device in light of this new evidence, and examine the Cellebrite device itself.”

“Cellebrite has been around for a while but I feel like prosecutors and police officers have become much more comfortable with it,” Rozas told Gizmodo over the phone. Previously, data extraction was primarily used in only certain types of cases—typically child pornography or, sometimes, drug offenses. Now, however, cops’ first move is typically to find some sort of incriminating evidence on a suspect’s cell phone, he said, regardless of what kind of case it is.
The widespread use of such tools is potentially concerning, given one of the more outlandish claims made in Marlinspike’s blog: that corrupted apps on a targeted phone could basically overwrite any data extracted by Cellebrite’s tools—essentially making it possible for an outside party to manipulate data on confiscated devices.
Despite how large these security issues seem to be, legal experts aren’t necessarily sold on the idea that they will change anything. Megan Graham, who is a Clinical Supervising Attorney at the Samuelson Law, Technology & Public Policy Clinic with Berkeley Law School, said that it wasn’t totally clear how the revelations about Cellebrite’s technology could affect court cases. In all likelihood, they probably won’t do a whole lot for older cases, though there may be some discussion moving forward about how better to address potential issues with police technology, she said.
“I think it’s going to take a while to figure out what the exact legal ramifications of this are,” said Graham in a phone call. “I don’t know how likely it is that cases would be thrown out,” she said, adding that a person who has already been convicted would likely have to “show that someone else identified this vulnerability and exploited it at the time”—not an especially easy task.
“Going forward, I think it’s just hard to tell,” Graham said. “We now know that this vulnerability exists, and it creates concerns about the security of Cellebrite devices and the integrity of evidence.” But there’s a lot that we don’t know, she emphasized. Among Graham’s concerns, she said that “we don’t know if the vulnerability is being exploited,” and that makes it difficult to discern when it could become an issue in past cases.
Ultimately, Graham said she was hopeful that in the future courts may try to be more thoughtful and nuanced about how they approach digital evidence—something this whole incident could help catalyze: “I think there will be cases where defense attorneys are able to get judges engaged [on this issue]. They will present the security concerns, worries about manipulated evidence, and it might be persuasive. I think there will be a wide array of responses when it comes to how this plays out in cases,” she said.
Cellebrite allegedly pushed out new updates to its products on Monday, Vice News reports. The company claimed that the patches had “been released to address a recently identified security vulnerability. The security patch strengthens the protections of the solutions.” However, Vice also reports that the company did not “specifically say whether the addressed vulnerability is one and the same as the one disclosed by Marlinspike.”